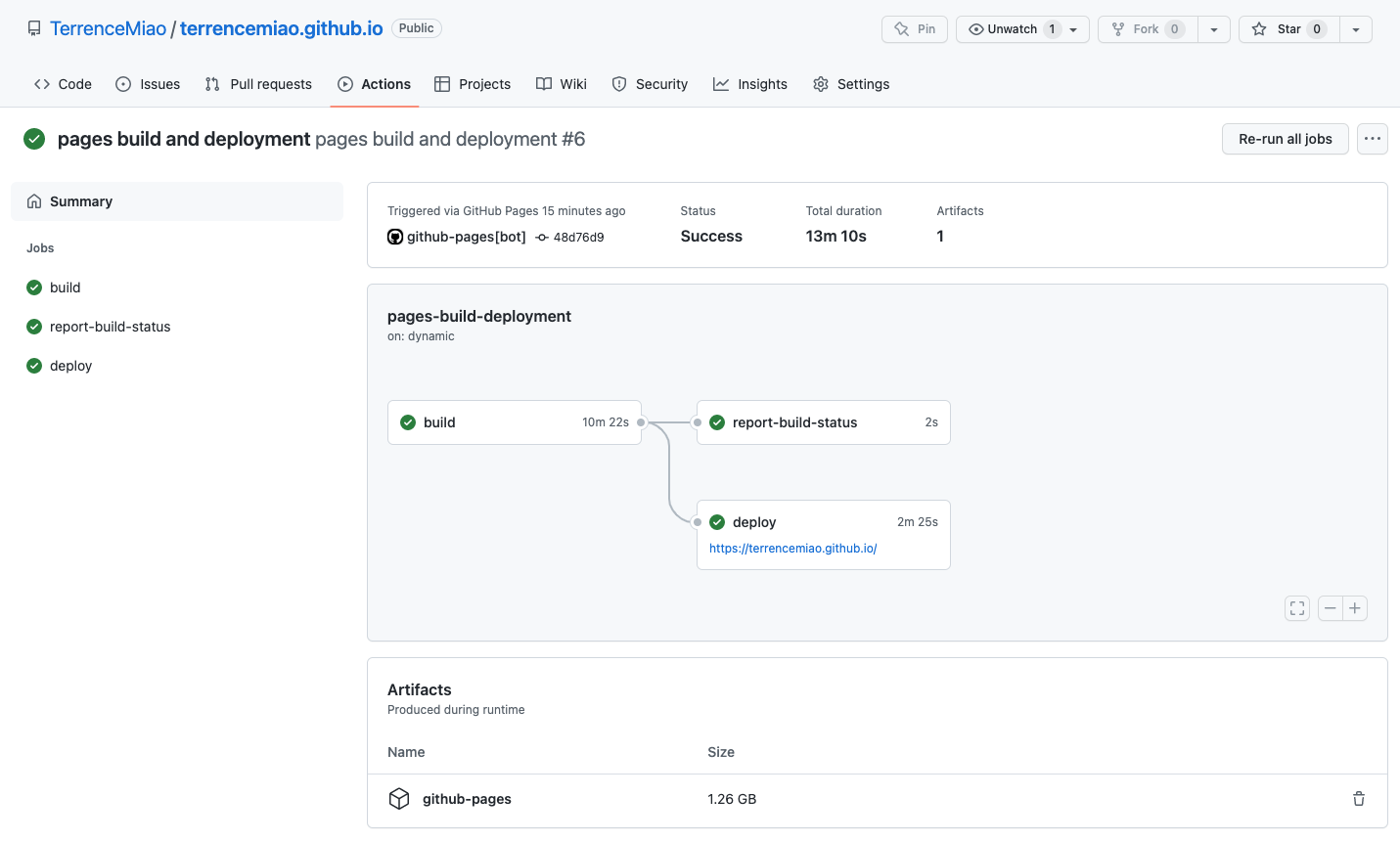
Bondi Beach in Upscayl
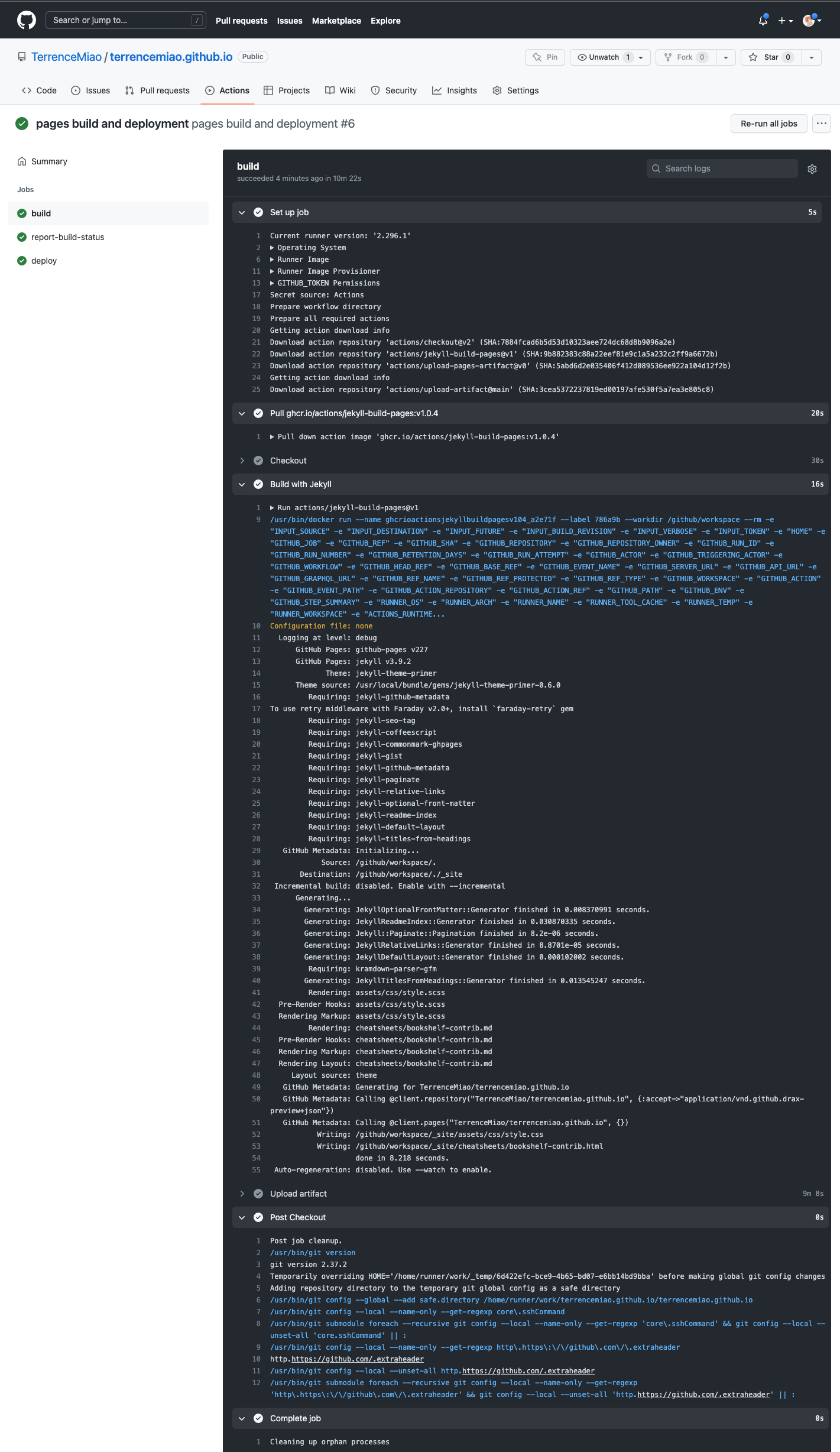
Bondi Beach original

Bondi Beach upscayled

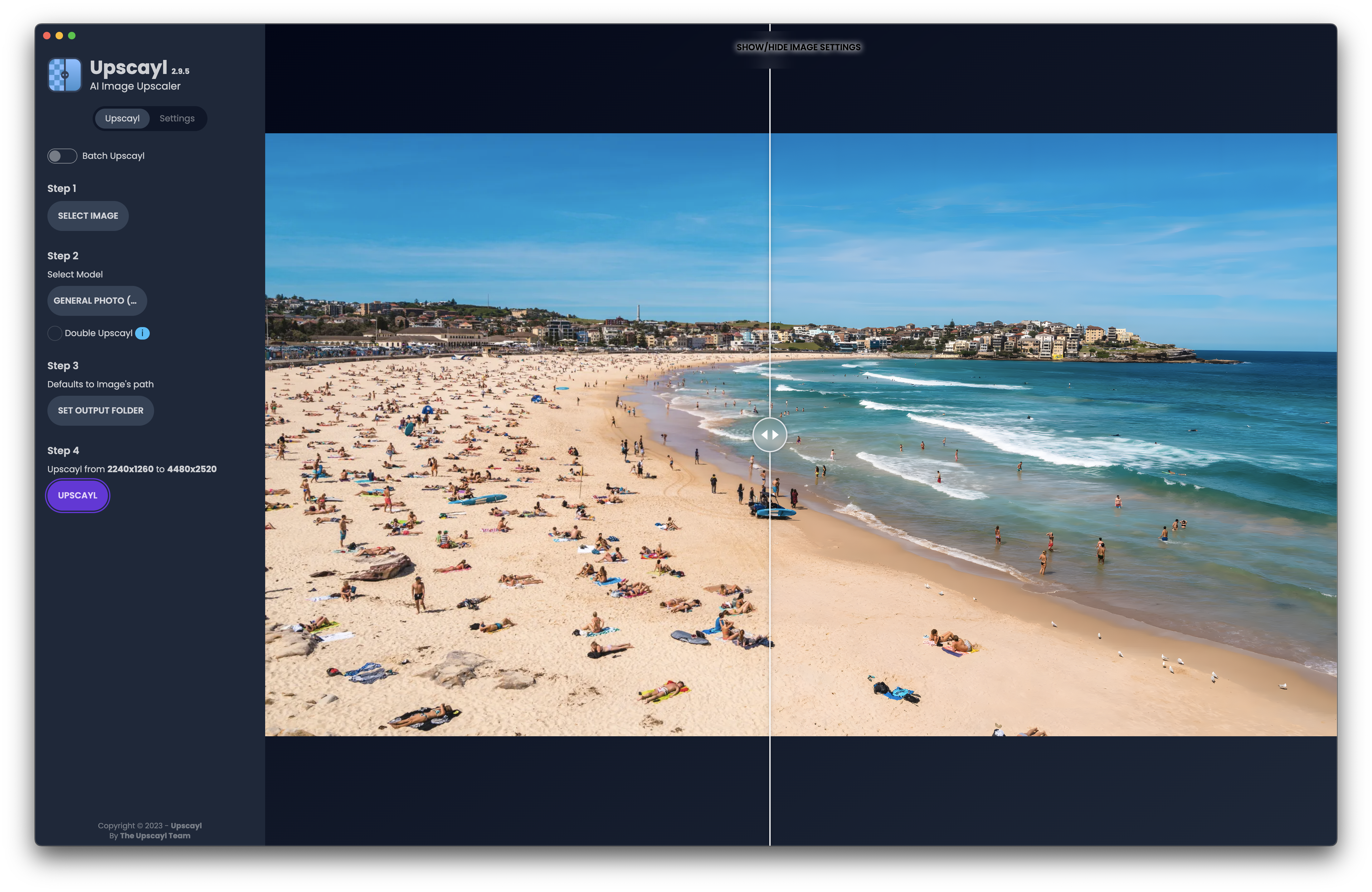
Young Girl in Upscayl
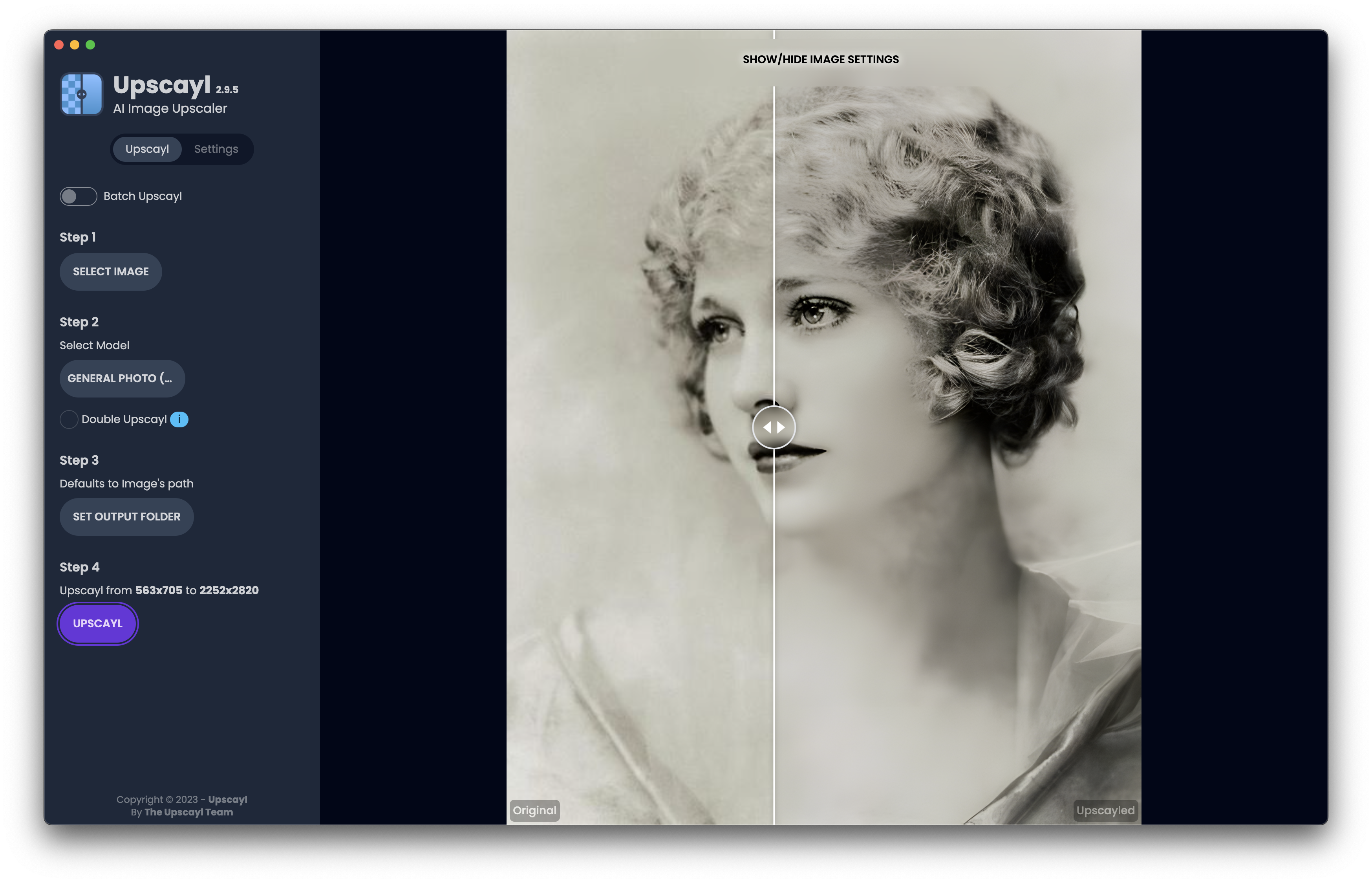
Young Girl original

Young Girl upscayled

References
- Upscayl - AI Image Upscaler, https://www.upscayl.org/
Bondi Beach in Upscayl
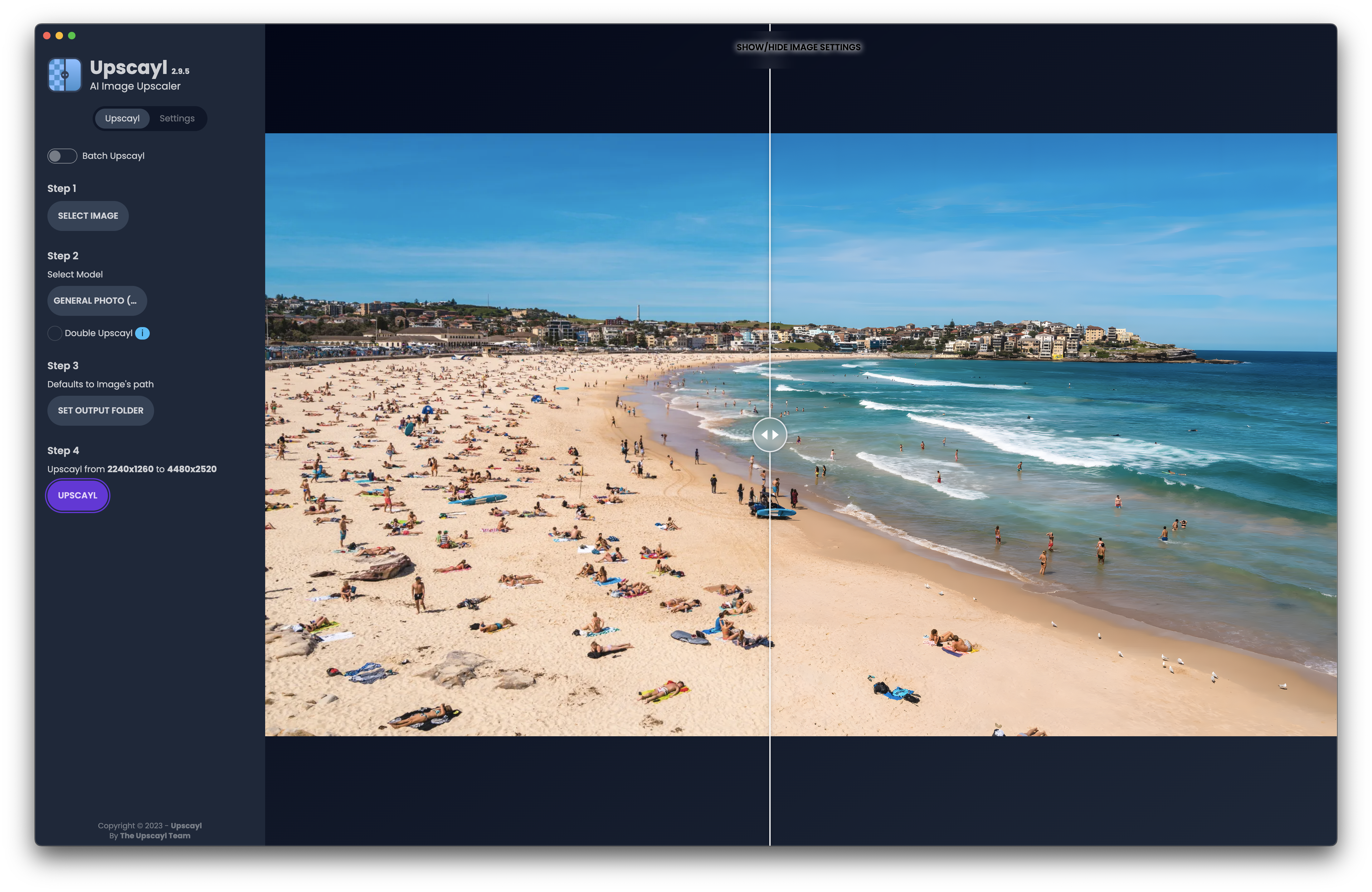
Bondi Beach original

Bondi Beach upscayled

Young Girl in Upscayl
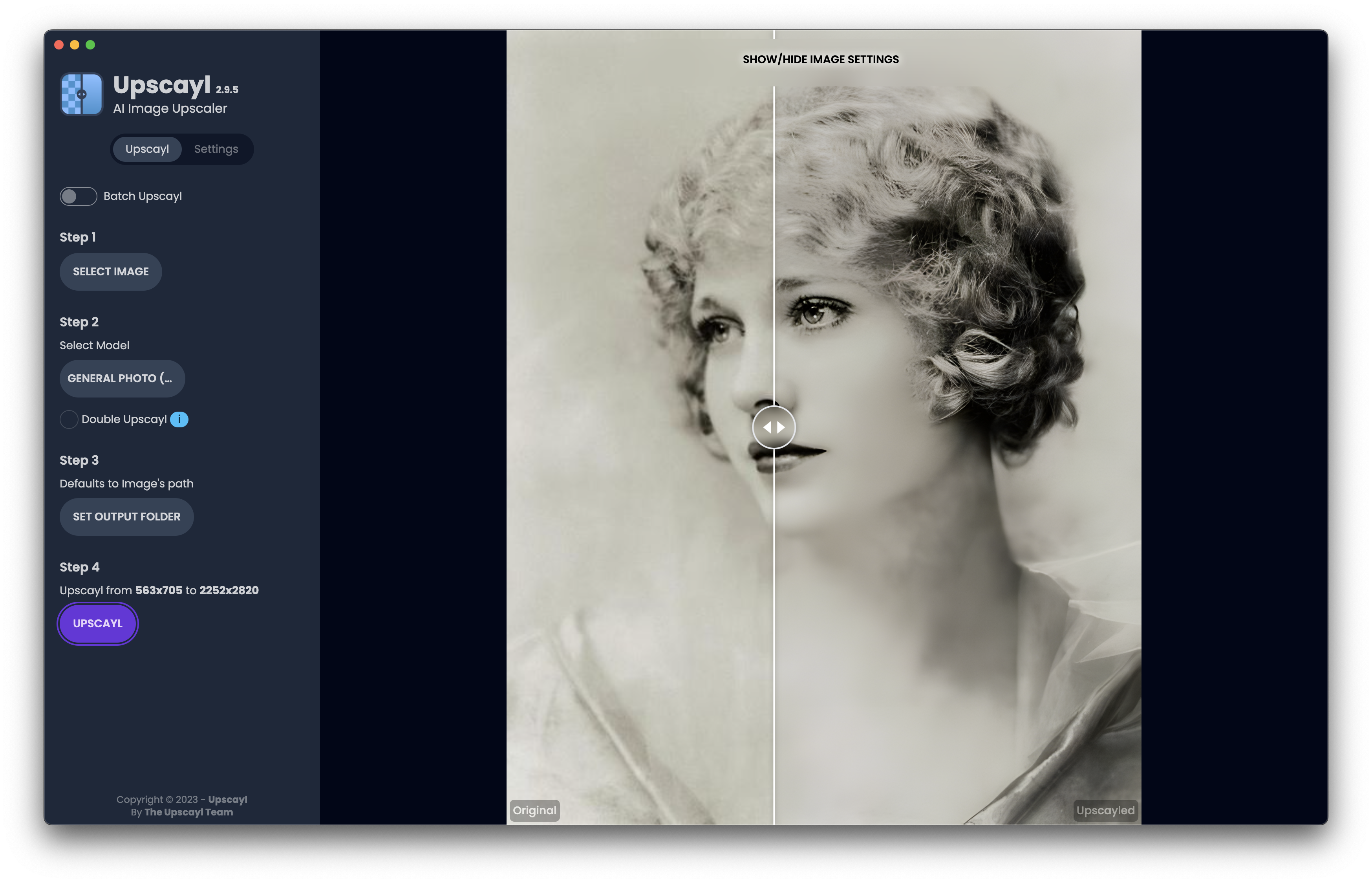
Young Girl original

Young Girl upscayled

Want to run OpenSSH Server on Windows e.g. Windows 10. From Windows 10, it natively supports OpenSSH.
NOTE: The beta and nightly build of OpenSSH Server for Windows have a lot of runtime issues.
Check OpenSSH installation:
1 | PS C:\ProgramData\ssh> Get-WindowsCapability -Online | Where-Object Name -like 'OpenSSH*' |
Install the missing OpenSSH Server:
1 | PS C:\ProgramData\ssh> Add-WindowsCapability -Online -Name OpenSSH.Server~~~~0.0.1.0 |
Check OpenSSH for Windows version, check Windows Operating System version:
1 | PS C:\ProgramData\ssh> ((Get-Item (Get-Command sshd).Source).VersionInfo.FileVersion) |
Check Windows Domain information:
1 | PS C:\ProgramData\ssh> dsregcmd /status |
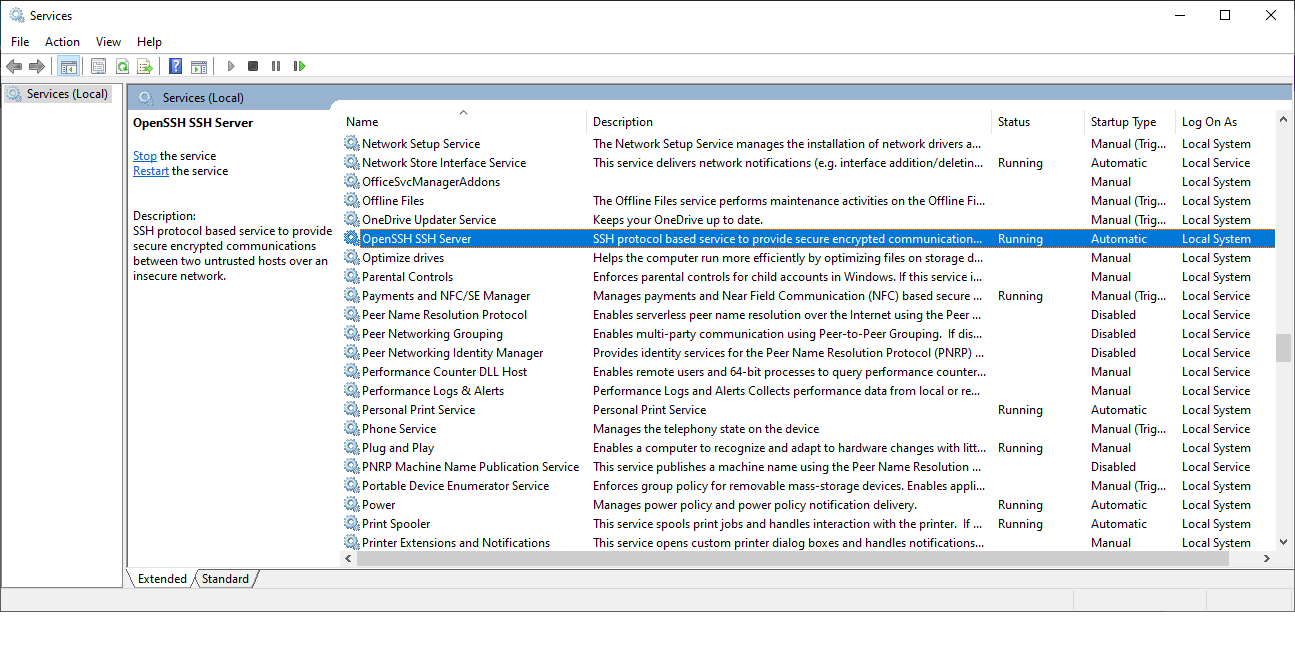
Check OpenSSH Server for Windows run as a service:
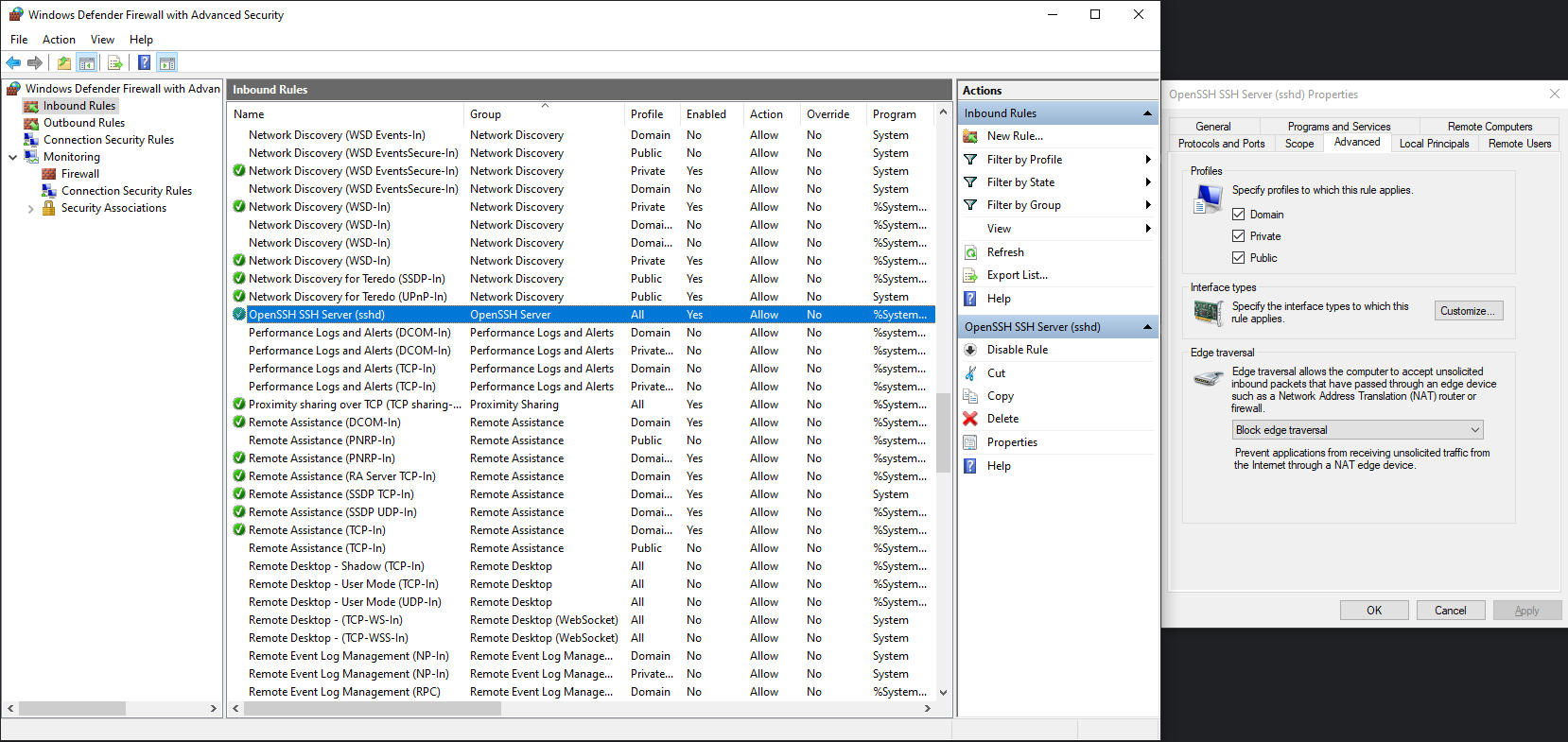
Make sure OpenSSH SSH Server firewall inbound rule allows ALL profiles:
The default C:\ProgramData\ssh\sshd_config file doesn’t work for Windows Domain users authentication, and does’t support .ssh\authorized_keys public key authentication. Error lookup_principal_name: User principal name lokup failed for user ‘corp\darling’ in OpenSSH Server C:\ProgramData\ssh\logs\ssd log file. A work around solution is to comment out lines:
1 | #Match Group administrators |
A complete sshd_config example file:
1 | # This is the sshd server system-wide configuration file. See |
Now run ssh client and log on SSH Server:
1 | sshpass -f ~/.ssh/windows.passwd ssh -l darling windows.local |
Host windows.local has VPN connection which is granted with git repository.
1 | ssh-copy-id -i id_rsa.pub darling@windows.local |
If PasswordAuthentication is enforced, and pubilc key authentication in SSH Server is not supported, try:
1 | sshpass -f ~/.ssh/windows.passwd ssh -D 3128 -q -C -N -f darling@windows.local |
git with Sock/Socks5 proxy1 | git config http.proxy 'socks5://localhost:3128' |
Then can access git repository via proxy both on command line and in UI client.
NOTE: Some SSH Server doesn’t allow public key authentication. Then sshpass is a friend here for you.
Install sshpass in MacOS:
1 | brew install esolitos/ipa/sshpass |
Test sshpass:
1 | $ ssh -oProxyCommand="sshpass -f ~/.ssh/windows.passwd ssh -W %h:%p jumphost" -l darling jumphost-npe.paradise.net |
Setup .ssh/config file:
1 | ## Keeping SSH Sessions Alive |
Righ model, right tools - the new way of building and collaborating on frontend apps is the core element of Micro Frontends.
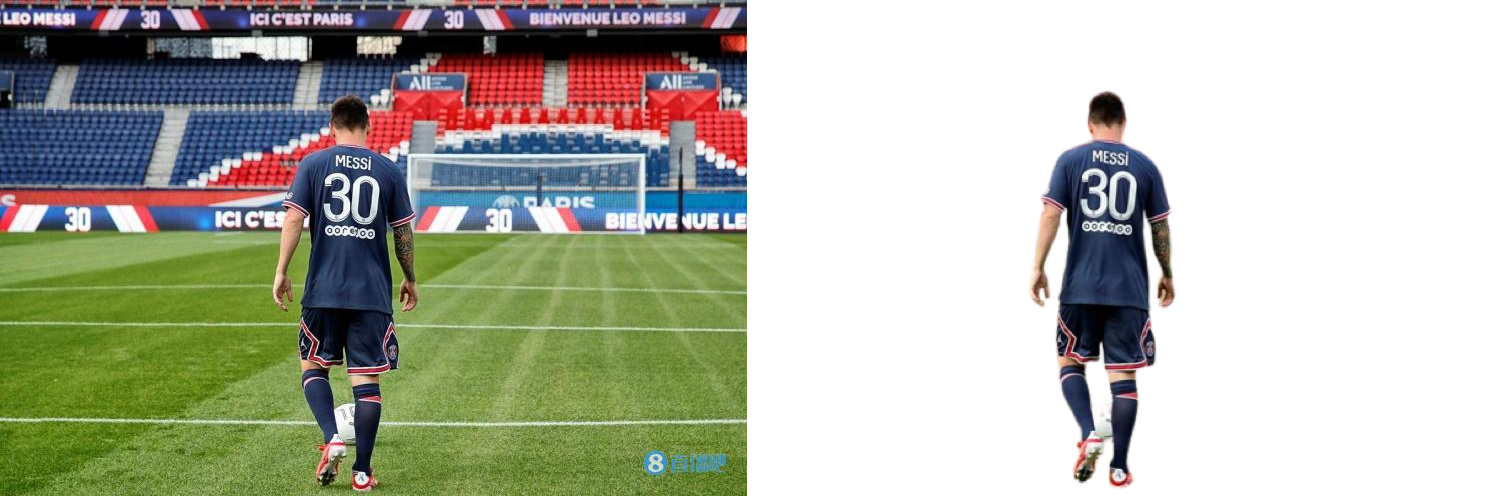
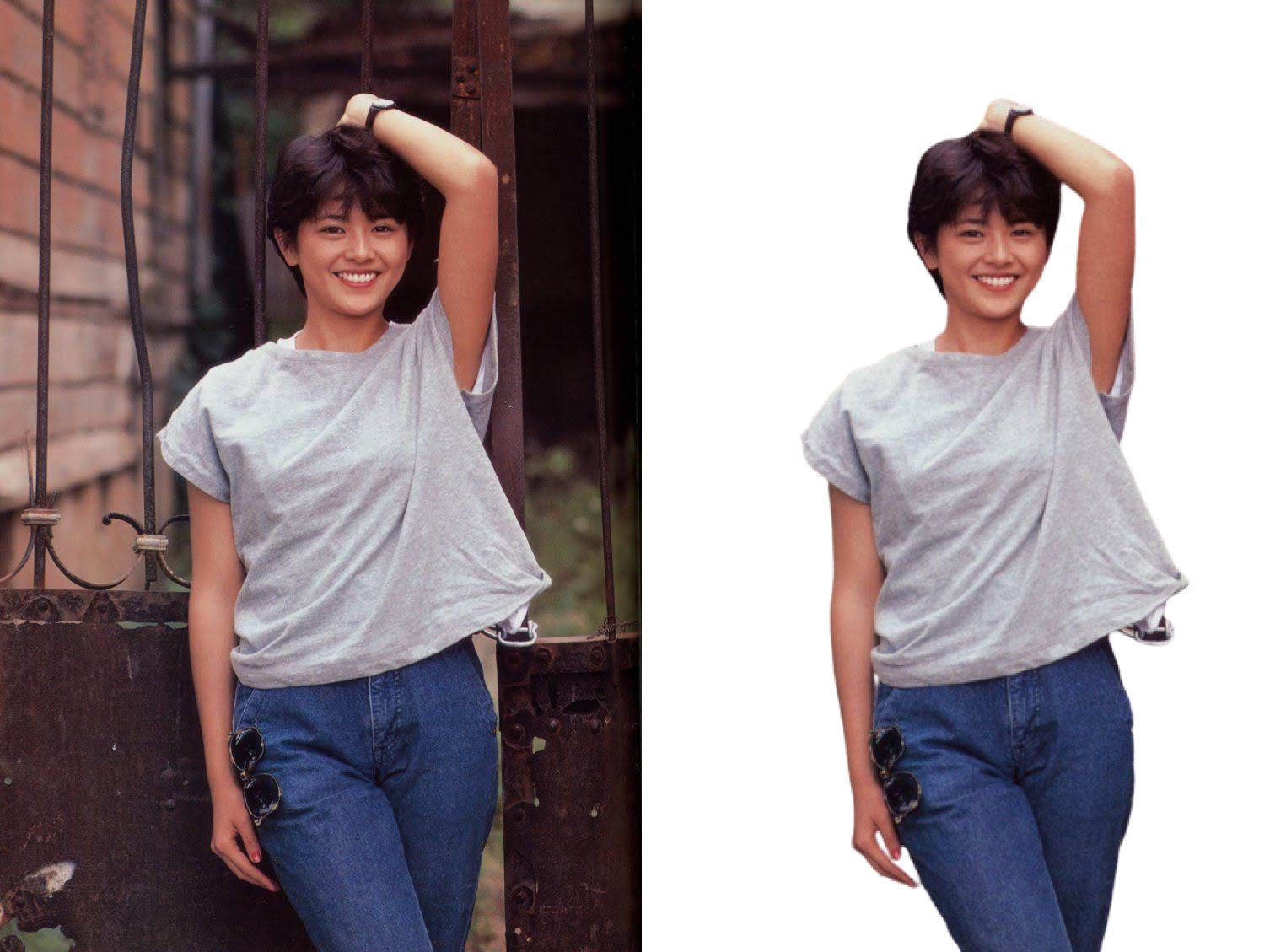
Remove backgrounds 100% automatically in 5 seconds with one click. Thanks to remove.bg https://www.remove.bg/ clever AI.
Geekbench head to head - Mac vs iPad vs Android:
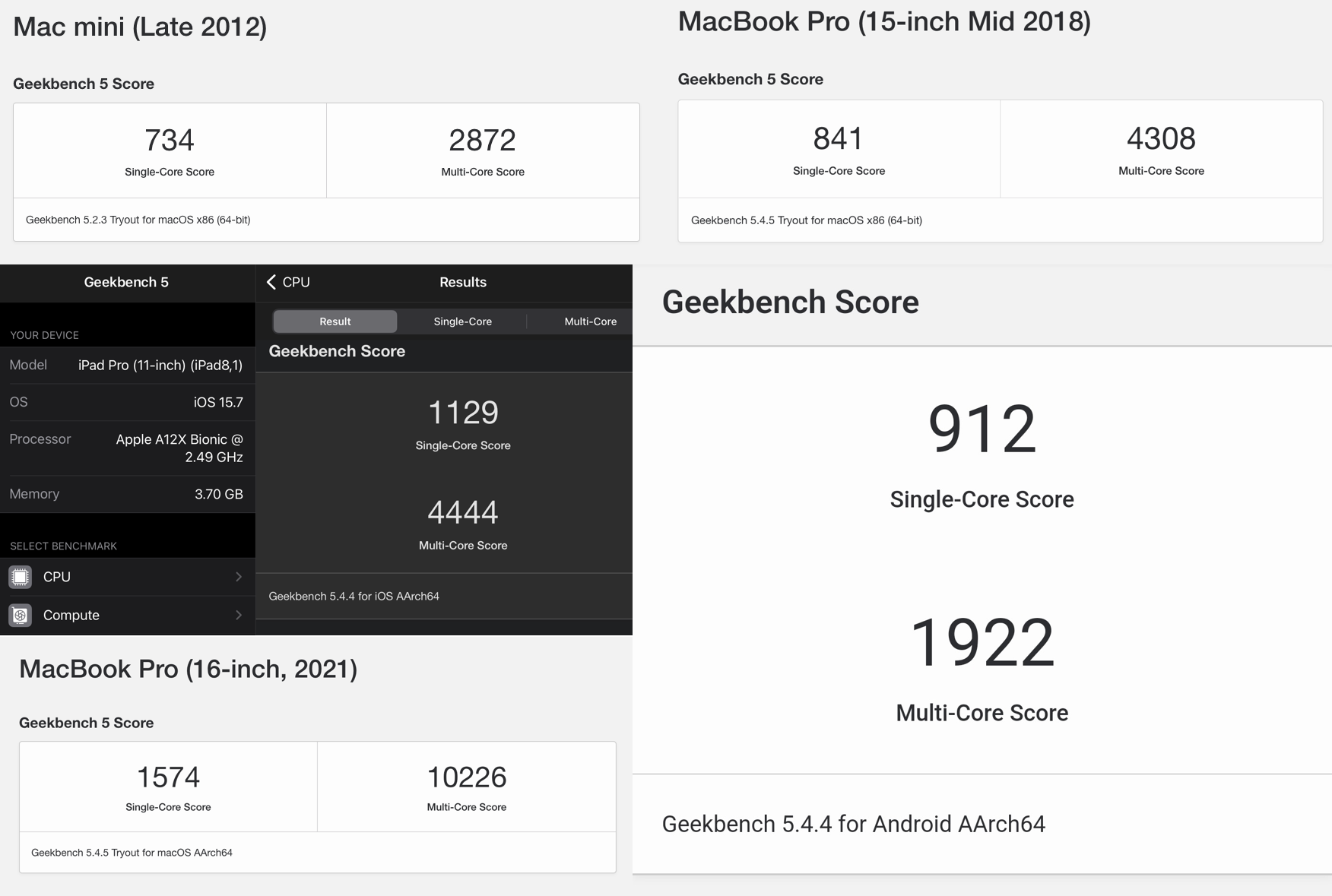
Conclusion:
ARM vs x86 谁是未来,一目了然。
NOTE
The Apple M1 chip is built for Macs, and the A15 for phones. They use completely different architectures. The A15 prioritizes battery over performance. The M1 has more firepower for graphics.
Prerequisites:
Step by step:


Have you tried GitHub Actions?